RMM (Remote Monitoring and Management) is a critical component of modern cybersecurity strategies. It involves the use of software agents deployed on endpoints (such as servers, workstations, and mobile devices) that allow IT administrators to remotely monitor, manage, and secure these devices.
RMM tools provide a centralized dashboard that enables IT teams to proactively identify and address security vulnerabilities, patch software, detect and respond to security incidents, and perform routine maintenance tasks. The benefits of using RMM include improved security posture, reduced downtime, and increased IT efficiency. Historically, RMM solutions have evolved from traditional network management systems to encompass a wider range of security-related features.
In this article, we will explore the various aspects of RMM in cybersecurity, including its key features, benefits, and best practices. We will also discuss how RMM can be integrated with other security technologies to create a robust and comprehensive cybersecurity defense system.
The Role of RMM in Cybersecurity
RMM plays a crucial role in cybersecurity by providing IT administrators with the tools and capabilities to effectively monitor, manage, and secure endpoints. Key aspects of RMM in cybersecurity include:
- Endpoint visibility: RMM provides a comprehensive view of all endpoints on the network, including their hardware and software inventory, patch status, and security configurations.
- Remote access: RMM allows IT administrators to remotely access endpoints to troubleshoot issues, install software, and perform other administrative tasks.
- Patch management: RMM can automate the process of patching software vulnerabilities, which is critical for preventing security breaches.
- Security monitoring: RMM can monitor endpoints for suspicious activity, such as unauthorized access attempts, malware infections, and data breaches.
- Incident response: RMM can help IT administrators quickly identify and respond to security incidents, minimizing their impact.
- Compliance reporting: RMM can generate reports that demonstrate compliance with industry regulations and standards, such as PCI DSS and HIPAA.
- Improved efficiency: RMM can automate many routine IT tasks, freeing up IT administrators to focus on more strategic initiatives.
- Reduced downtime: RMM can help prevent and minimize downtime by proactively identifying and addressing potential issues.
These key aspects of RMM work together to provide organizations with a comprehensive and effective cybersecurity solution. By leveraging RMM, organizations can improve their security posture, reduce their risk of data breaches, and maintain a high level of operational efficiency.
Endpoint visibility
Endpoint visibility is a critical aspect of RMM’s role in cybersecurity. By providing a comprehensive view of all endpoints on the network, RMM enables IT administrators to proactively identify and address security vulnerabilities, ensuring the overall security posture of the organization.
- Inventory management: RMM helps organizations maintain an accurate inventory of all hardware and software assets on their network. This information is essential for tracking license compliance, managing software updates, and identifying potential security risks.
- Patch management: RMM can automate the process of patching software vulnerabilities, which is critical for preventing security breaches. By keeping software up to date, organizations can reduce their exposure to known vulnerabilities that could be exploited by attackers.
- Security configuration management: RMM allows IT administrators to enforce security configurations on all endpoints. This ensures that endpoints are configured in a secure manner and meet industry best practices.
- Endpoint monitoring: RMM can monitor endpoints for suspicious activity, such as unauthorized access attempts, malware infections, and data breaches. This enables IT administrators to quickly identify and respond to security incidents, minimizing their impact.
By providing endpoint visibility, RMM empowers IT administrators with the information and tools they need to effectively secure their networks. Endpoint visibility is a fundamental component of RMM’s role in cybersecurity, enabling organizations to proactively identify and address security risks, maintain compliance, and ensure the overall security of their IT infrastructure.
Remote access
Remote access is a critical aspect of RMM’s role in cybersecurity, as it enables IT administrators to perform essential tasks without having to be physically present at each endpoint. This capability is especially valuable in situations where endpoints are geographically dispersed or when rapid response is required to address security incidents.
- Troubleshooting: Remote access allows IT administrators to remotely troubleshoot issues with endpoints, such as hardware failures, software errors, and network connectivity problems. This can significantly reduce downtime and improve the overall efficiency of IT support.
- Software installation and updates: RMM can be used to remotely install software updates and patches on endpoints. This ensures that endpoints are running the latest versions of software, which is essential for maintaining security and preventing vulnerabilities.
- Security monitoring and incident response: Remote access enables IT administrators to remotely monitor endpoints for security threats and incidents. This allows them to quickly identify and respond to security breaches, minimizing the impact to the organization.
- Administrative tasks: RMM can be used to perform a variety of administrative tasks on endpoints, such as resetting passwords, managing user accounts, and configuring security settings. This can save IT administrators a significant amount of time and effort.
Overall, remote access is a key feature of RMM that enables IT administrators to effectively manage and secure endpoints, regardless of their location. By providing remote access capabilities, RMM enhances the efficiency and effectiveness of IT support, reduces downtime, and improves the overall security posture of the organization.
Patch management
In the context of cybersecurity, patch management plays a pivotal role in safeguarding systems against vulnerabilities that could lead to security breaches. RMM solutions offer automated patch management capabilities that enable IT administrators to efficiently and effectively apply software updates across all endpoints within their network.
- Vulnerability Reduction: Software vulnerabilities are common entry points for cyberattacks. By automating the patching process, RMM proactively addresses these vulnerabilities, minimizing the risk of successful exploitation.
- Improved Security Posture: Regular patching ensures that software is up-to-date with the latest security fixes, enhancing the overall security posture of endpoints and the network as a whole.
- Compliance Adherence: Automated patch management helps organizations maintain compliance with industry regulations and standards, such as PCI DSS and HIPAA, which require timely patching of software.
- Reduced Downtime: Minimizing software vulnerabilities reduces the likelihood of security breaches that can lead to system downtime. Automated patching further streamlines the process, ensuring minimal disruption to business operations.
In summary, the automated patch management capabilities of RMM are a cornerstone of effective cybersecurity practices. By proactively addressing software vulnerabilities, improving security posture, ensuring compliance, and reducing downtime, RMM plays a critical role in safeguarding organizations against cyber threats.
Security monitoring
Security monitoring is a critical aspect of RMM’s role in cybersecurity. By continuously monitoring endpoints for suspicious activity, RMM helps organizations to identify and respond to security threats promptly, minimizing their impact and protecting sensitive data.
- Real-time threat detection: RMM can monitor endpoints in real-time, using advanced threat detection algorithms to identify suspicious activity, such as unauthorized access attempts, malware infections, and data breaches. This enables organizations to respond quickly to security threats, preventing them from causing significant damage.
- Endpoint visibility: RMM provides IT administrators with a comprehensive view of all endpoints on the network, including their security configurations, software inventory, and patch status. This visibility enables IT administrators to identify and address potential security risks before they can be exploited by attackers.
- Centralized management: RMM provides a centralized platform for managing security monitoring and incident response across all endpoints. This simplifies the process of managing security and ensures that all endpoints are protected.
- Improved security posture: By continuously monitoring endpoints for suspicious activity and addressing potential security risks, RMM helps organizations to improve their overall security posture and reduce their risk of data breaches.
In summary, security monitoring is a core component of RMM’s role in cybersecurity. By providing real-time threat detection, endpoint visibility, centralized management, and improved security posture, RMM helps organizations to protect their data and systems from cyber threats.
Incident response
Incident response is a critical aspect of RMM’s role in cybersecurity, as it enables organizations to quickly and effectively respond to security threats, minimizing their impact and protecting sensitive data.
- Rapid detection and response: RMM provides real-time monitoring and threat detection capabilities, enabling IT administrators to quickly identify and respond to security incidents as they occur. This rapid response time is crucial for minimizing the impact of security breaches and preventing them from causing significant damage.
- Centralized management: RMM provides a centralized platform for managing security incident response across all endpoints. This simplifies the process of managing security incidents and ensures that all endpoints are protected.
- Automated remediation: RMM can automate certain aspects of security incident response, such as isolating infected endpoints, blocking malicious traffic, and restoring affected systems. This automation can save IT administrators valuable time and effort, allowing them to focus on more complex tasks.
- Improved security posture: By enabling organizations to quickly and effectively respond to security incidents, RMM helps to improve their overall security posture and reduce their risk of data breaches.
In summary, incident response is a key component of RMM’s role in cybersecurity. By providing rapid detection and response, centralized management, automated remediation, and improved security posture, RMM helps organizations to protect their data and systems from cyber threats.
Compliance reporting
Compliance reporting is an essential aspect of RMM’s role in cybersecurity as it enables organizations to demonstrate their adherence to industry regulations and standards, such as PCI DSS and HIPAA. These regulations are designed to protect sensitive data and ensure the security of financial and healthcare information.
RMM solutions provide comprehensive reporting capabilities that allow organizations to track their compliance status and generate reports that can be used to demonstrate compliance to auditors and regulatory bodies. These reports provide detailed information about the security measures that have been implemented, such as patch management, security configurations, and incident response procedures.
By leveraging RMM for compliance reporting, organizations can streamline their compliance efforts, reduce the risk of non-compliance, and improve their overall security posture. Compliance reporting is a critical component of RMM’s role in cybersecurity, as it helps organizations to maintain trust with customers and partners, avoid penalties, and protect their reputation.
Improved efficiency
In the context of cybersecurity, improved efficiency plays a pivotal role in empowering IT administrators to effectively manage and secure their networks. RMM solutions offer a range of automation capabilities that streamline routine IT tasks, such as:
- Automated patch management
- Remote software installation and updates
- Security configuration management
- Endpoint monitoring and alerting
By automating these tasks, RMM frees up IT administrators from the burden of repetitive and time-consuming manual processes, allowing them to focus their efforts on more strategic initiatives that drive business value.
The practical significance of improved efficiency in cybersecurity cannot be overstated. With limited resources and the ever-increasing volume of security threats, IT administrators are constantly under pressure to maintain a high level of security while also meeting the demands of the business. RMM’s automation capabilities alleviate this pressure, enabling IT administrators to optimize their time and resources, and ultimately enhance the overall security posture of the organization.
In summary, improved efficiency is a crucial component of RMM’s role in cybersecurity. By automating routine IT tasks, RMM empowers IT administrators to be more proactive, strategic, and effective in their efforts to protect the organization from cyber threats.
Reduced downtime
In the realm of cybersecurity, reduced downtime is of paramount importance. Downtime can lead to significant financial losses, reputational damage, and disruption of critical operations. RMM plays a vital role in minimizing downtime by proactively identifying and addressing potential issues before they escalate into major disruptions.
- Early detection and prevention: RMM solutions continuously monitor endpoints for potential issues, such as hardware failures, software conflicts, and security vulnerabilities. By identifying these issues early on, IT administrators can take proactive measures to prevent them from causing downtime.
- Automated remediation: RMM can be configured to automatically remediate certain issues, such as applying software patches, updating drivers, and restarting services. This automation reduces the time and effort required to resolve issues, minimizing the risk of downtime.
- Remote access and troubleshooting: RMM provides IT administrators with remote access to endpoints, enabling them to troubleshoot and resolve issues remotely. This eliminates the need for on-site visits, reducing the time it takes to resolve issues and minimizing downtime.
- Improved security: RMM helps to improve overall security by identifying and addressing security vulnerabilities. By keeping software up to date, enforcing security configurations, and monitoring for suspicious activity, RMM reduces the risk of security breaches and other incidents that can lead to downtime.
In summary, reduced downtime is a critical aspect of RMM’s role in cybersecurity. By proactively identifying and addressing potential issues, RMM helps organizations to minimize downtime, maintain business continuity, and protect their reputation.
FAQs on the Role of RMM in Cybersecurity
This section presents frequently asked questions (FAQs) and their answers to provide a deeper understanding of the role of Remote Monitoring and Management (RMM) in cybersecurity.
Question 1: What are the key benefits of using RMM for cybersecurity?
Answer: RMM offers numerous benefits, including improved security posture, reduced downtime, increased IT efficiency, enhanced visibility and control, and simplified compliance reporting.
Question 2: How does RMM help organizations improve their security posture?
Answer: RMM strengthens security by providing centralized visibility and control over endpoints, enabling proactive patch management, enforcing security configurations, monitoring for suspicious activity, and automating incident response.
Question 3: Can RMM help organizations reduce downtime?
Answer: Yes, RMM plays a crucial role in minimizing downtime by proactively identifying and addressing potential issues, automating remediation tasks, providing remote access for troubleshooting, and improving overall security.
Question 4: How does RMM enhance IT efficiency?
Answer: RMM streamlines IT operations by automating routine tasks, centralizing management, and providing remote access capabilities, allowing IT administrators to focus on strategic initiatives.
Question 5: What are the key features of RMM solutions?
Answer: Common features include endpoint monitoring, remote access, patch management, security configuration management, vulnerability scanning, automated remediation, and reporting capabilities.
Question 6: Is RMM a necessary tool for modern cybersecurity strategies?
Answer: Yes, RMM has become an indispensable tool for organizations seeking to enhance their cybersecurity posture, improve efficiency, and reduce the risk of downtime.
Summary: RMM plays a vital role in modern cybersecurity strategies, providing organizations with comprehensive capabilities to monitor, manage, and secure their IT infrastructure. Its benefits include improved security, reduced downtime, enhanced efficiency, and simplified compliance.
Transition: To delve deeper into the technical aspects and best practices of RMM in cybersecurity, please continue to the next section of this article.
Tips for Leveraging RMM for Effective Cybersecurity
To maximize the benefits of RMM in cybersecurity, organizations should consider the following best practices:
Tip 1: Prioritize Endpoint Security: Focus on securing endpoints, as they represent the primary targets for cyberattacks. Implement robust endpoint protection measures, including antivirus software, firewalls, and intrusion detection systems.
Tip 2: Establish Patch Management Policies: Regularly patch software vulnerabilities to prevent attackers from exploiting them. Configure RMM to automate patch deployment and ensure timely updates across all endpoints.
Tip 3: Enforce Security Configurations: Establish and enforce security configurations for endpoints to prevent misconfigurations that could create security gaps. Use RMM to centrally manage and monitor security settings.
Tip 4: Implement Multi-Factor Authentication: Enhance login security by enabling multi-factor authentication for remote access and privileged accounts. This adds an extra layer of protection against unauthorized access.
Tip 5: Monitor Network Traffic: Utilize RMM’s network monitoring capabilities to detect suspicious network activity. Set up alerts to identify anomalies and potential threats in real-time.
Tip 6: Automate Incident Response: Configure RMM to automate incident response tasks, such as isolating infected endpoints, blocking malicious traffic, and generating alerts. This speeds up response times and minimizes the impact of security breaches.
Tip 7: Conduct Regular Security Audits: Regularly conduct security audits to assess the effectiveness of RMM and identify areas for improvement. This helps organizations stay ahead of evolving threats and maintain a strong security posture.
Tip 8: Provide Regular Security Awareness Training: Educate employees about cybersecurity best practices to prevent them from falling victim to phishing attacks and social engineering scams.
By following these tips, organizations can harness the full potential of RMM to enhance their cybersecurity posture, protect against cyber threats, and ensure the integrity and availability of their IT infrastructure.
Conclusion
In the ever-evolving cybersecurity landscape, the role of Remote Monitoring and Management (RMM) has become indispensable. RMM provides organizations with a comprehensive solution to monitor, manage, and secure their IT infrastructure, proactively addressing security vulnerabilities and minimizing the risks associated with cyber threats.
This article has explored the various aspects of RMM in cybersecurity, including its key features, benefits, and best practices. By implementing RMM effectively, organizations can enhance their security posture, improve IT efficiency, reduce downtime, and maintain compliance with industry regulations. It is crucial for organizations to embrace RMM as a fundamental component of their cybersecurity strategies to protect their valuable data and assets from malicious actors.
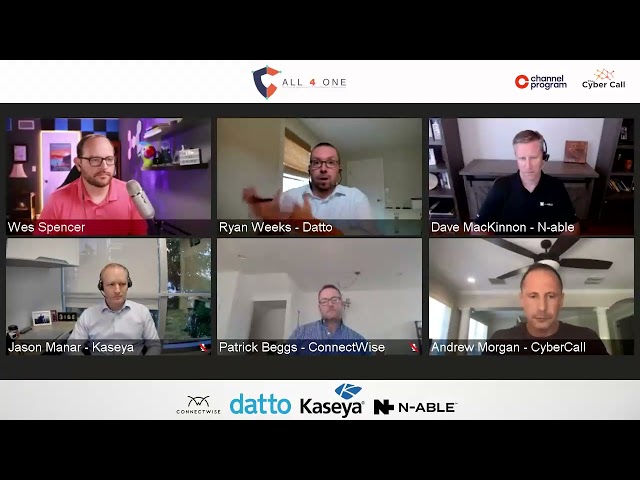
Youtube Video: